

Any camera that uses the V4L2 system on Linux. So, mostly webcams.
One important note is that IP cams are not supported yet, but I’d like to add support for them.
I’m Hunter Perrin. I’m a software engineer.
I wrote an email service: https://port87.com
I write free software: https://github.com/sciactive


Any camera that uses the V4L2 system on Linux. So, mostly webcams.
One important note is that IP cams are not supported yet, but I’d like to add support for them.


I’m working on one called Soteria. It’s still early in development, but I’m focusing on both privacy and cloud availability.
It uses any WebDAV store to upload footage, but it’s designed to work best with my own WebDAV server Nephele. This lets it upload footage to any S3 compatible blob storage, end to end encrypted.
That way if your cameras go offline, you can watch the last footage they were able to upload.
Like I said, it’s in early development, so it’s not yet ready to use, but I’m going to be putting more work into it soon and try to get it to a place where you can use it.
It works with any V4L2 compatible camera, so laptops, webcams, and Raspberry Pi cameras should all work.


Is it called Flick-fil-A?
Cool, CVEs don’t tell you whether it’s remotely exploitable. What I’m talking about is an issue with the Linux kernel itself that can be exploited without having the existing ability to run code on the machine.
It’s very big news when there’s a vulnerability in the Linux kernel itself that can be remotely exploited. Like, everyone on any security show/podcast/blog is talking about it.
Sure, but those vulnerabilities aren’t just open to the network. Almost every one requires you to be able to run at least unprivileged arbitrary code on the machine.
How vulnerable your system is with an old kernel/old code depends on what you’re running. If you’re running a bunch of sophisticated services that allow access on the open internet, you may have more vulnerabilities than if you’re just running a file share. The kernel doesn’t really matter at all unless either you allow other people to run commands or someone is able to exploit a RCE exploit.


I transferred my entire NAS storage, which includes all of my backups, cloud files, my family’s backups, and my… Linux ISOs. That was about 12TB.
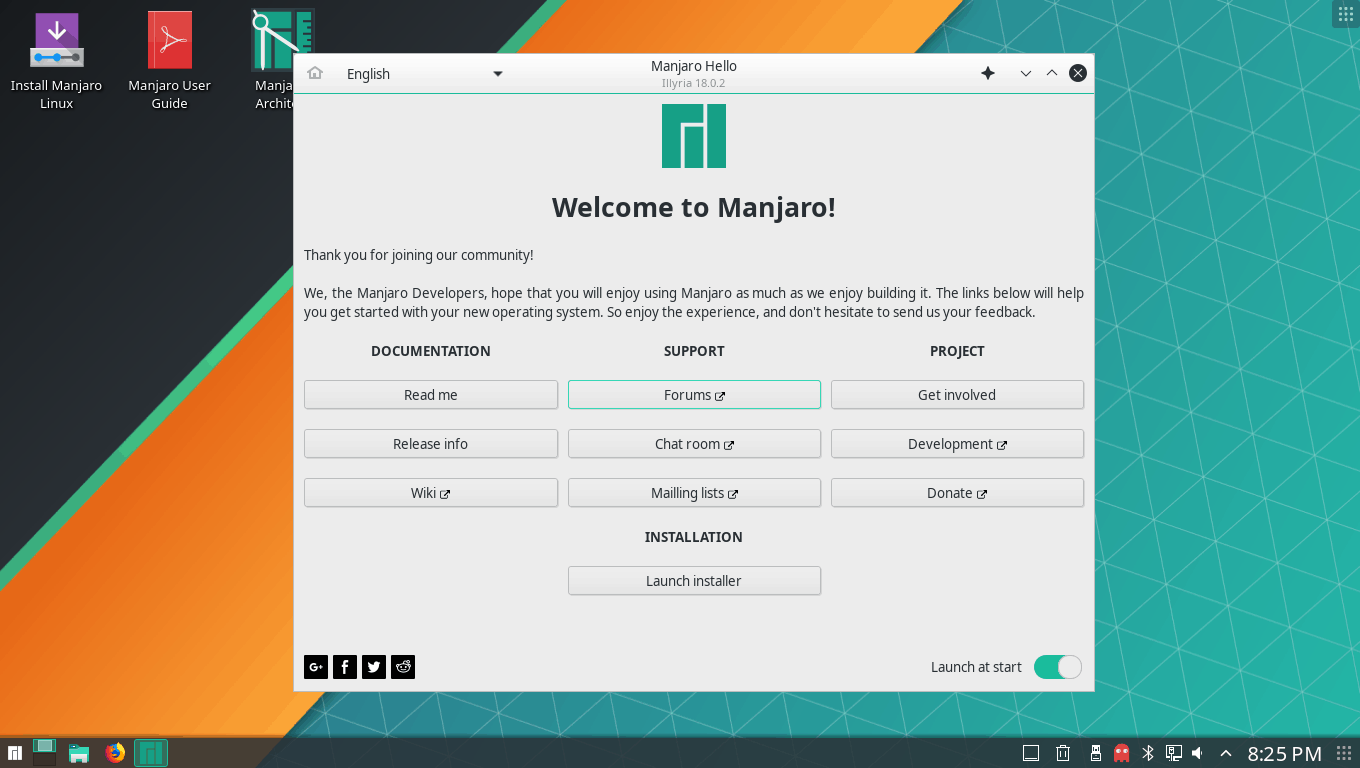
Or as I’ve started called it recently, Google+ Linux.
More like, Mom can we get Arch btw?
No we have Arch btw at home.
Arch btw at home:


Remember when Google+ had billions of users because Google counted Gmail users as Google+ users?


I cannot add that many layers to a physical burger.

You gotta remember that any form of energy only needs to be less damaging than the alternative to be better. When the alternative is coal, every other form of energy is less damaging.


I’ve tried to move as much as I can into Flatpak. That way I can just copy my .var folder, and all my apps are migrated.
For other things like my configs, I use a git repo.
I use Proxmox for the machine that I use to download all of the Linux ISOs I want. You know, with a VPN, through BitTorrent. Linux ISOs.


The original 3, “.cum”, “.nut”, and “.orgasm”.


Missed the opportunity for .myshit.
Why are you running servers with a data store on a partition that you mount on multiple operating systems?
I release a lot of my software in GitHub and I’m offended at how accurate this is.